IP (Internet Protocol) is a set of rules for how information is sent over the internet. There are billions of digital devices connected to the internet, and they all have a unique IP address, which ensures their unique location. It is important to understand how the Internet Protocol functions since the threats prevalent on the Internet communicate via the same protocol.
Cybersecurity experts use IP information in a number of ways to help protect the network and prevent unauthorized access to data and devices. Here, we will discuss some important ways cybersecurity experts use IP information, such as threat intelligence and access control.
Threat Actor Intelligence and Analysis
Cybersecurity experts are important as they protect the digital ecosystem and, therefore, use IP addresses to identify any looming danger. IP addresses, which act as the unique code of identification for various devices, help to get information about the attacker and thus play an important role as a threat actor intelligence. Moreover, with information related to an IP address, experts can identify the patterns, give warning signs of attacks, and give prediction-related predictions to future attacks. This intelligence helps develop defenses against known and emerging threats.
Network Security
IP addresses act as the code of identification for the devices connected over the internet and thus play a crucial role in managing network security. IP information is of great use in setting up firewalls that act as barriers, thereby controlling traffic into and out of the network. This means that expert IP monitors can specify attempts at gaining access without authority and, therefore, block any traffic that could be harmful to the network. To know the IP address of your devices, use services such as What is My IP.
Managed Detection and Immediate Response
In a world full of cybersecurity threats, managed detection and immediate responses are crucial and for this, cybersecurity experts use IP addresses. The experts can easily detect and take prompt action against any threat or unauthorized activity by using IP addresses. This ensures that your data and devices remain safe and secure. Moreover, inspection of IP information helps in observing the real source of the attack, knowing the nature of the attacks, and taking appropriate response measures.
Access Control
Access control also plays an essential role in preventing unauthorized access and various cybersecurity threats. Cybersecurity experts take advantage of IP information to set up digital access controls. Once set, the controls would ensure that none but the devices of a permitted IP address would have access to the areas of the network that are sensitive. Thus, controlling access forms a crucial measure in the prevention of unauthorized persons’ access to data and its subsequent leaks.
-
Yamaha Blue Fest Officially Begins from April 10 in NepalHIGHLIGHTS Yamaha Nepal kicked off the Yamaha Blue Fest with exciting offers on bikes and…
-
Redmi A5 Arriving Soon in Nepal: Lowest in Price, Highest in Refresh RateHIGHLIGHTS Redmi A5 4G price in Nepal could be Rs. 11,999 (3/64GB) and Rs. 13,999…
-
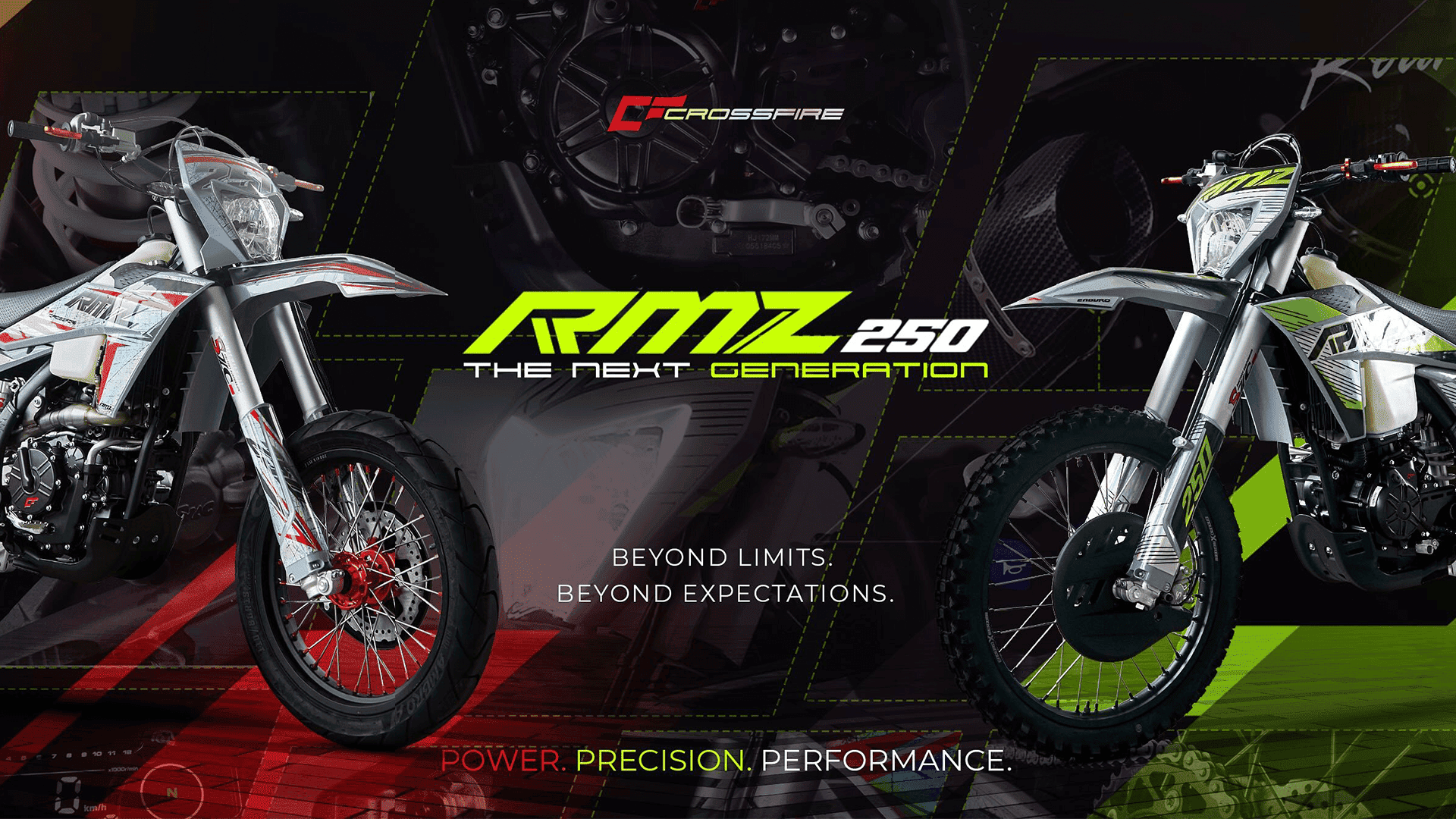
Crossfire RMZ 250 Now in Nepal: What’s New Compared to the Outgoing RM 250?HIGHLIGHTS Crossfire RMZ 250 price in Nepal is Rs. 8.59 Lakhs. RMZ 250 is the…